The Ivory Tower Isn't Tweeting
- By Dian Schaffhauser
- 04/09/14
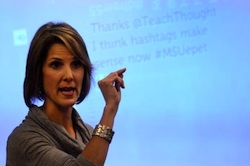
Michigan State University Assistant Professor Christine Greenhow Said it's "troubling" that academics don't use social media to share academic work with the public in greater numbers. |
If social media is the means by which organizations open dialogs and make themselves more accessible, transparent and accountable, higher education is being left behind, say two researchers from Michigan State University.
In a report published in the March 2014 issue of British Journal of Educational Technology, Christine Greenhow, an assistant professor in the College of Education, and Benjamin Gleason, a doctoral student of education, examined the use of popular social media services by academics and found their practices lacking. In a survey of 1,600 researchers, they reported that 15 percent of respondents use Twitter for professional purposes, 28 percent use YouTube and 39 percent use Facebook. The way those services are primarily used is to find collaborators and disseminate scholarly work or the work of others. It's not to reach out to students for the purposes of instruction.
Greenhow finds that "troubling," she said in a statement, since universities are trying to increase access to publicly funded research. "Only a minority of university researchers are using free and widely available social media to get their results and published insights out and into the hands of the public, even though the mission of public universities is to create knowledge that makes a difference in people's lives," she said. "Simply put, there's not much tweeting from the ivory tower."
While some faculty members are sharing their work in social media, the researchers promote the idea of universities adopting policies that reward such behaviors as it considers tenure and promotion practices. "Academia is not serving as a model of social media use or preparing future faculty to do this," said Greenhow.
About the Author
Dian Schaffhauser is a former senior contributing editor for 1105 Media's education publications THE Journal, Campus Technology and Spaces4Learning.